This three-part blog series will explore threat-based methodology and how it benefits every company with a network. The series leverages the analysis presented by the Federal Risk and Authorization Management Program (FedRAMP) Program Management Office (PMO) in conjunction with the National Institute of Standards and Technology (NIST).
The FedRAMP PMO and NIST collaborated to complete an analysis of the NIST 800-53 Rev 5 controls, scoring each control using the MITRE ATT&CK framework to determine its Protection Value. For more information, you can read their blog post “FedRAMP Updates the Threat-Based Methodology to Authorizations.” Additional details are available in their GitHub account.
While the FedRAMP PMO is focused on how to leverage this methodology within the FedRAMP risk-analysis process, the methodology applies to everyone interested in protecting their computer network. The analysis looked at each control and scored it according to how well that control protects against specific MITRE ATT&CK techniques, resulting in a prioritized list of controls with scores from 208.86 to 0.
This gives companies specific controls that, if implemented, will provide the most protection for the effort. While general in nature, they are a great start. Every network will be unique with a unique risk posture, which may alter the protection value of any control.
What jumped out at me when I first looked at this list was the gap between the top seven controls and those ranked eighth and below. There is a 28.56-point gap between number seven and number eight, which is a 13% difference. Additionally, the top seven controls are all related to the capabilities and benefits of Devo.
Here’s the top-seven list:
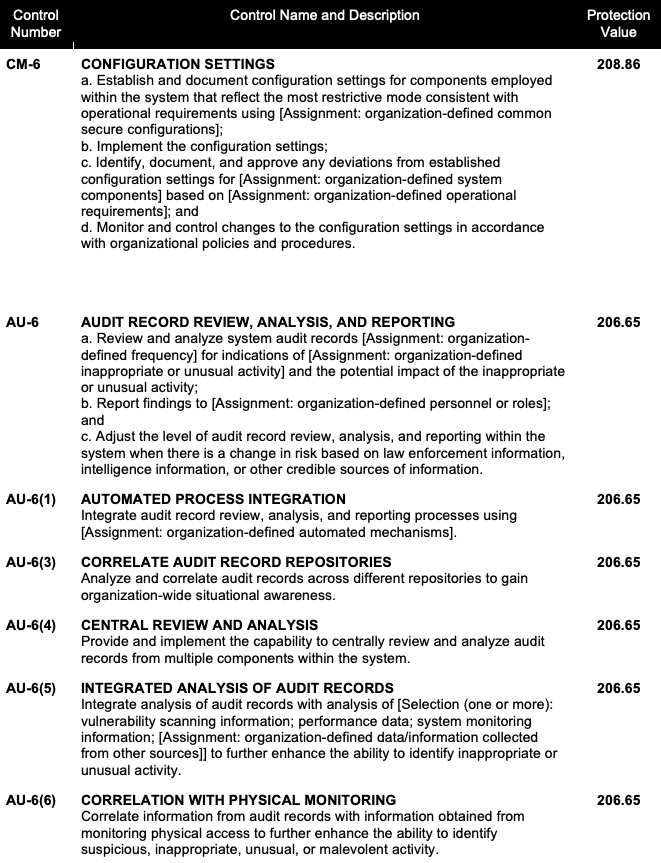
The second post in the series will take a closer look at CM-6. The final post will examine AU-6 and it’s subcontrols.



