Navigating the SIEM Landscape: A Buyer’s Guide for Security Leaders

Gain a singular view of your risk posture, security operations, and threat detection. Leverage MITRE ATT&CK framework context, Devo-engineered security content, and automated enrichments and correlations across cloud, hybrid, and on-premises security environments.
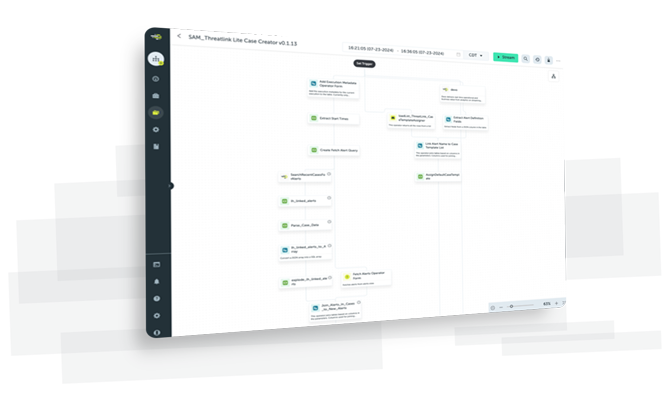
Use AI-powered playbooks and decision automation to proactively safeguard your organization against threats. Benefit from automated triage, no-code SOAR playbooks, intuitive investigations, and case management. Experience a lightning-speed time to value–most customers see a return on investment within 30 days.
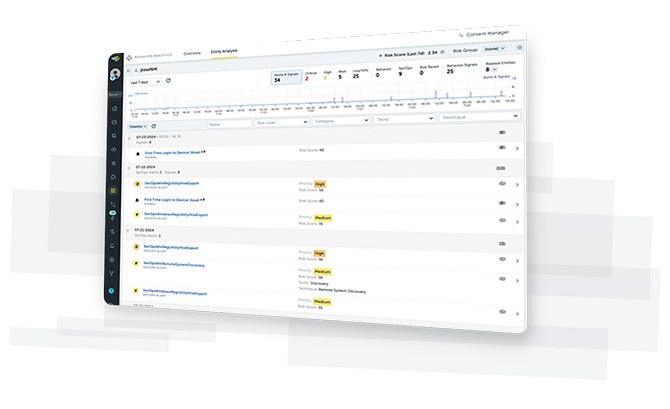
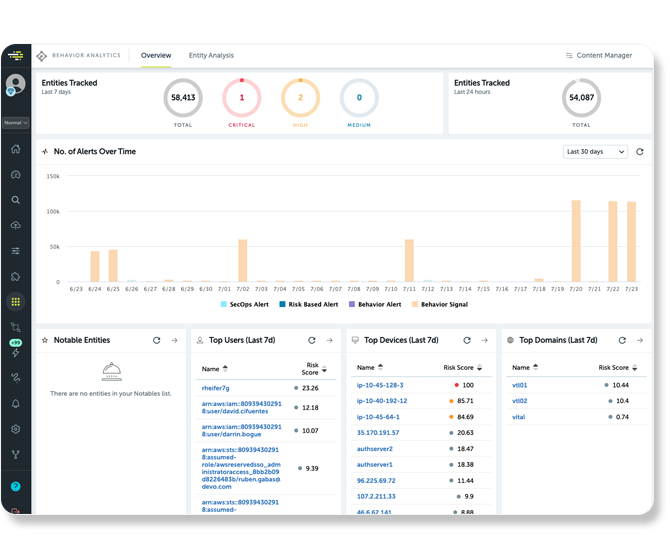
Devo Behavior Analytics uncovers anomalous activity across users, devices, and domains within multi-petabyte datasets. It employs an extensive library of AI models to detect unusual behaviors and quantify risks to streamline investigations.

By combining cutting-edge analytics and AI, you can supercharge your threat analysis and identification. Analysts are empowered to autonomously perform investigations at machine speed, enabling them to respond quickly to emerging threats.
Unleash the power of your SOC with integrated SIEM, SOAR and UEBA.
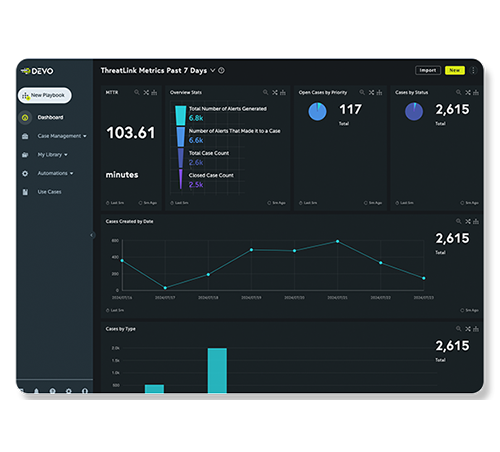
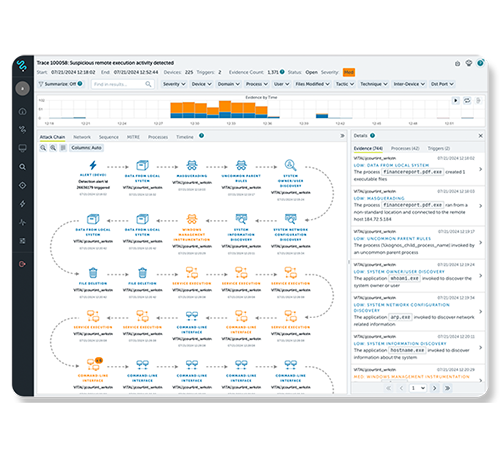
Devo ThreatLink™ automates alert triage, streamlines incident response, and optimizes SOC efficiency for proactive security.
Autonomously investigate suspicious activity using attack-tracing AI.
Devo Behavior Analytics employs an extensive library of AI models to detect unusual behaviors and quantify risks to streamline investigations.