Organizations cannot wonder if a data breach will happen — they must prepare for when that day comes. Early detection is key to mitigating an attack when it inevitably occurs, but how can CISOs ensure their teams can sift through all the noise they encounter in the SOC to spot malicious activity? Security information and event management (SIEM) technology can play a critical role in empowering your security team to detect potential indicators of compromise faster.
However, SIEMs have historically been a costly investment for organizations, and it takes a long time to realize value from legacy solutions. While legacy SIEMs were designed to consolidate and centralize relevant security data, too many had rigid features that made them ineffective at sifting through the noise to bubble up the most important information for high-fidelity detections. Because of this shortcoming, time to value was measured in months to years — which doesn’t cut it today.
SIEMs have certainly come a long way, but many SIEM deployment initiatives still lack clear goals and don’t have the necessary stakeholder buy-in needed for success. Devo, a flexible cloud-native next-gen SIEM that combines threat intelligence content streaming, gives your security team the foundation it needs to successfully implement a use case-driven approach to SIEM adoption and deployment. This method unites stakeholders around desired business outcomes so the SIEM is implemented to surface the most important information first, reducing the time to value and eliminating pressure from key stakeholders.
How Devo Reduces Time to Value
According to the Gartner® report, How to Deploy a SIEM Solution Successfully, SIEM buyers should “implement a suitable architecture to address where the business and its IT are operating.” Throughout the pandemic, more organizations have shifted to the cloud, so their SIEM should be a cloud-native solution, too. Devo is a cloud-native solution that requires little support for immediate deployment while also providing a true single pane of glass view to security teams.
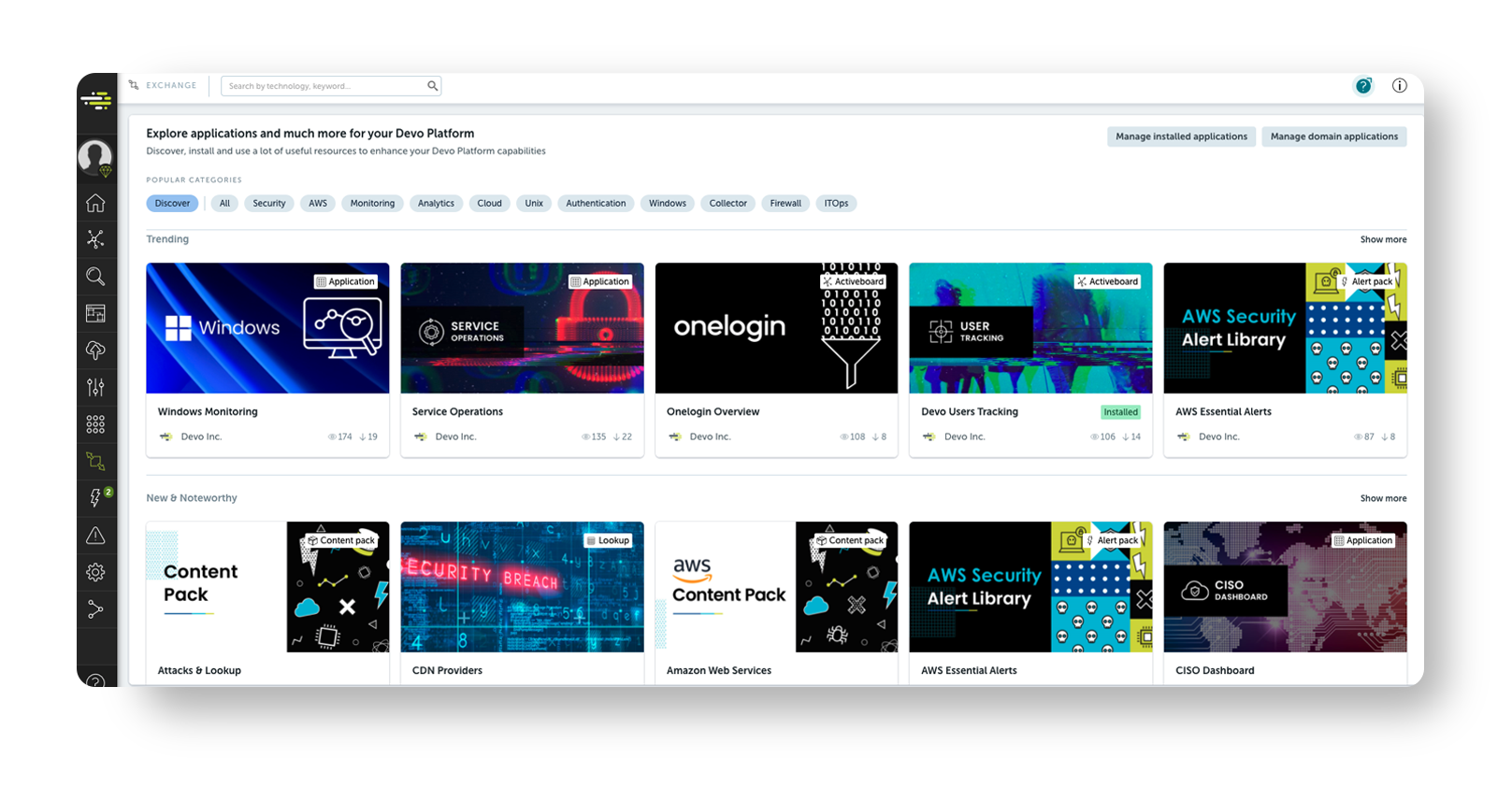
Because of Devo’s targeted, use case-driven approach and flexible features that enable your security team to ingest data from any of your sources, it’s much easier to deploy than a traditional SIEM. Whether data is from on-premises or cloud environments, Devo easily ingests it so that security analysts can obtain full visibility. Devo Security Operations can also seamlessly integrate with your existing security ecosystem to enrich investigations with valuable context. It also boasts flexible APIs so your team can connect to its preferred third-party tools. Devo not only easily ingests data and scales but also unlocks historical visibility with 400 days of always-hot data. The Platform’s flexibility also enables security teams to focus on what is most important: Detecting threats and protecting the business. Devo makes it easy to organize detections and responses and clearly defines actions to reduce the mean time to contain (MTTC) a threat and increase the fidelity of outputs. This prioritization significantly reduces the time to value, as it forces the security team to focus on the risks they need to mitigate first.
How Devo Can Measure Time to Value
As a result, Devo’s time to value is measured in days or weeks, not months or years. Devo also makes it easy to track and measure the value achieved. There is an overview dashboard built directly within Devo Security Operations. The Platform is also extremely flexible. For example, Devo customizable Activeboards help your team bring its data to life via intuitive and interactive dashboards.
Overall, Devo is truly a one-stop-shop for IT, operational and security departments. Its out-of-the-box flexibility enables organizations to prioritize the goals, KPIs and metrics that are most important while also enabling teams to prioritize their outputs and inputs. All of this empowers teams to improve their workflows, communicate their findings to the broader organization, and provide visibility at any department or role level. This makes it much faster and easier for security teams to meet their organization’s goals and objectives.
Evaluate Devo and other SIEM vendors in the new 2023 Buyer’s Guide to Next-Gen SIEM.
Citations
Gartner, How to Deploy a SIEM Solution Successfully, By Andrew Davies, Mitchell Schneider, Toby Bussa, Kelly Kavanagh, 7 July 2021.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.




